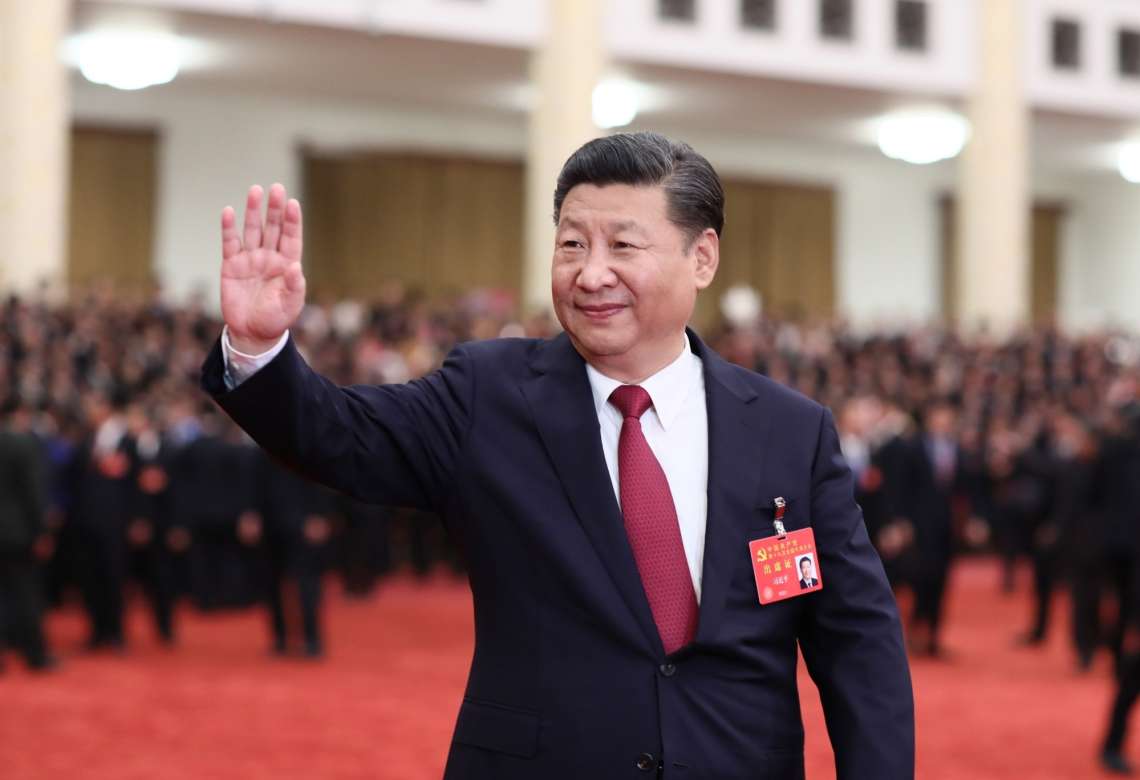
“The prolonged targeting of Indian power grid assets by Chinese state-linked groups offers limited economic espionage or traditional intelligence gathering opportunities,”….reports Asian Lite News
The power sector in India has been target in the recent month by a suspected state-sponsored Chinese hackers as part of an apparent cyber-espionage campaign, according to reports.
According to a report from the threat intelligence firm Recorded Future Inc., the hackers focused on at least seven “load dispatch” centers in northern India that are responsible for carrying out real-time operations for grid control and electricity dispersal in the areas they are located, near the disputed India-China border in Ladakh, the report said.
One of the load dispatch centers previously was the target of another hacking group, RedEcho, which Recorded Future has said shares “strong overlaps” with a hacking group that the US has tied to the Chinese government, it was reported.
“The prolonged targeting of Indian power grid assets by Chinese state-linked groups offers limited economic espionage or traditional intelligence gathering opportunities,” the Recorded Future report states. “We believe this is instead likely intended to enable information gathering surrounding critical infrastructure and/or pre-positioning for future activity.”

Meanwhile, a Chinese hacker group known as ‘Deep Panda’ that went into hibernation after attacking global entities some years ago, including in India, is back in action.
Deep Panda has launched new attacks against finance, travel and cosmetic industries since last month, exploiting Log4Shell open source software vulnerability to deploy the new Fire Chili rootkit.
During the past month, FortiGuard Labs researchers detected a campaign by a Chinese advanced persistent threat (APT) hacking group that has been active for at least a decade, targeting government, defence, healthcare, telecom, and financial organisations for data theft and surveillance.
Following exploitation, Deep Panda deployed a backdoor on the infected machines.
“Following forensic leads from the backdoor led us to discover a novel kernel rootkit signed with a stolen digital certificate. We found that the same certificate was also used by another Chinese APT group, named Winnti, to sign some of their tools,” the researchers said in a blog post.
The team attributed a series of opportunistic Log4Shell infections from the past month to Deep Panda.
“Though previous technical publications on Deep Panda were published more than half a decade ago, new findings relate to a more recent report about the Milestone backdoor, which shows that their operations have continued throughout all these years,” the researchers noted.
Amid heightened border tensions between India and China, cybersecurity researchers last year revealed a concerted campaign against India’s critical infrastructure, including the nation’s power grid, from Chinese state-sponsored groups.
The attacks, which coincided with the standoff between the two nations in May 2020, targeted a total of 12 firms, 10 of which were in the power generation and transmission sector.
According to a report in Recorded Future, the victims included a power plant run by National Thermal Power Corporation (NTPC) Limited and New Delhi-based Power System Operation Corporation Limited.
Investigators from the cybersecurity firm’s Insikt Group revealed the malware deployed by the threat actor shared similar infrastructure with other Chinese groups APT41 (Winnti or Wicked Panda) and Tonto Team.
FortiGuard said that Although both Deep Panda and Winnti are known to use rootkits as part of their toolset, “Fire Chili is a novel strain with a unique code base different from the ones previously affiliated with the groups”.
“The reason these tools are linked to two different groups is unclear at this time,” they noted.